1. Location Sharing: Guard Your Whereabouts
The allure of sharing your location with close friends is undeniable, yet caution is necessary. It’s essential to only share your whereabouts with people you trust. If you find location sharing bothersome, remember that you can always turn it off in the settings.
Furthermore, WhatsApp offers the flexibility to disable location sharing selectively, allowing you to retain privacy even among specific groups or individuals. When you deactivate location sharing:
- The concerned party won’t be able to track your current location.
- They will still have access to your last shared location until they modify their own settings.
- Step 1: Open WhatsApp and go to the chat with the person or group you want to adjust location sharing for.
- Step 2: Tap on the recipient’s/group’s name at the top of the chat window to access their profile.
- Step 3: Find the “Location” option and choose from the available settings: “Live Location,” “Share Live Location,” or “Send Your Current Location.”
- Step 4: Select “None” if you want to disable location sharing entirely for that person/group.
- Step 5: Repeat these steps for each person or group you want to manage location sharing for.
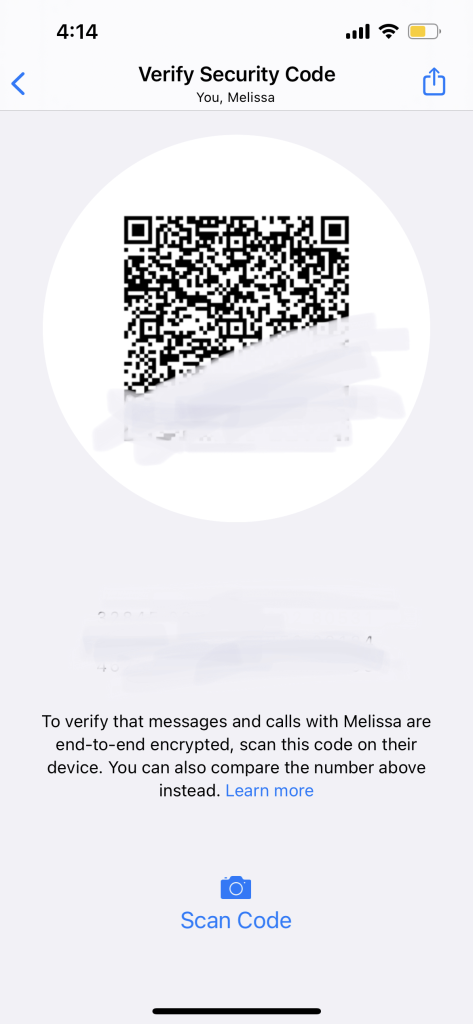
2. Encryption: A Shield for Private Conversations
Privacy and security thrive on encryption, and WhatsApp understands this. Every private conversation benefits from end-to-end encryption, safeguarding your messages from prying eyes. This feature is activated by default, ensuring your conversations remain exclusively between you and your intended recipient.
- Step 1: Open WhatsApp and navigate to the chat you want to secure.
- Step 2: Look for the lock icon at the top of the chat window; this indicates end-to-end encryption is active.
- Step 3: Engage in your private conversation knowing that your messages are protected by encryption.
3. Incognito Mode: Stealthy Conversations
When discretion is paramount, WhatsApp’s Incognito mode proves invaluable. This feature allows you to maintain private chats hidden from others using the app. Whether you’re sending confidential messages or simply want to converse without alerting anyone, Incognito mode has you covered.
- Step 1: Launch WhatsApp and open the chat with the person you want to message privately.
- Step 2: In the chat window, tap on the recipient’s name at the top.
- Step 3: Choose “Custom Notifications.”
- Step 4: Toggle on “Custom Notifications” and select options like “Hide Notification” or “Silent.”
- Step 5: Return to the chat, and your messages will be discreetly received without notifications.
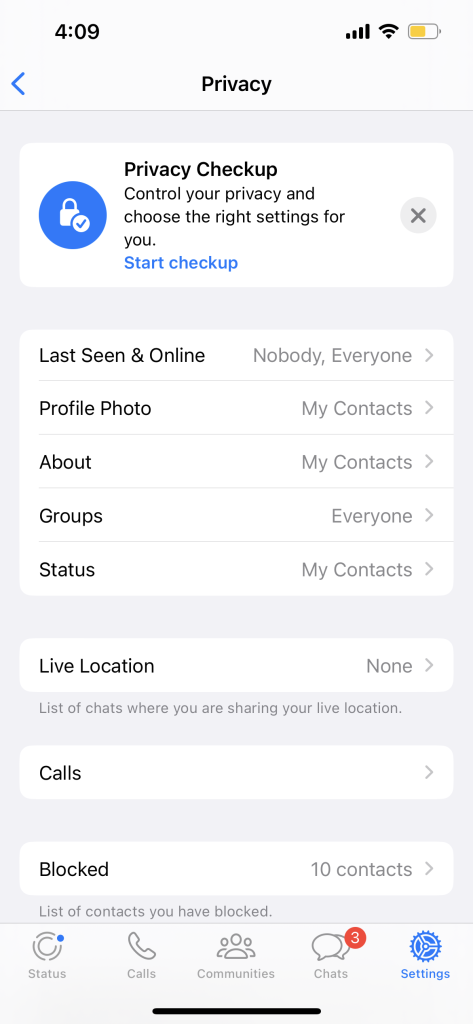
4. Preventive Measures: Know Your Sharing Boundaries
Awareness is key to preserving your privacy. Remember that whatever you share on WhatsApp is visible to your recipients. However, this doesn’t mean you’re sharing everything with everyone. By adjusting your privacy settings, you can manage who sees your content. If you’re using WhatsApp for sensitive discussions, consider enhancing your privacy with WireGuard VPN for end-to-end encrypted chats and added protection for your personal information.
- Step 1: Access WhatsApp’s settings by tapping the three dots in the upper-right corner of the main screen.
- Step 2: Select “Account,” then “Privacy.”
- Step 3: Explore settings like “Last Seen,” “Profile Photo,” “About,” and “Status.”
- Step 4: Choose from options like “Everyone,” “My Contacts,” or “Nobody” to control who sees your information.
- Step 5: Review and adjust these settings periodically to align with your privacy preferences.
5. WhatsApp Privacy Landscape: Room for Improvement
While WhatsApp offers valuable privacy features, some users might seek more comprehensive control over their data. The ability to hide your contacts list or restrict message visibility is currently limited. If you’re looking for heightened privacy options, explore alternatives like Wickr Me or Signal, which provide greater customization and control over who accesses your information.
- Step 1: Research alternative messaging apps like Wickr Me or Signal.
- Step 2: Download and install the chosen app from your app store.
- Step 3: Set up your account and explore the advanced privacy features offered.
- Step 4: Import your contacts if desired and start using the app for more privacy-conscious communications.
- Step 5: Keep informed about updates and improvements to ensure continued privacy.
6. Disappearing Messages: Enhancing Conversational Privacy
WhatsApp’s Disappearing Messages feature offers an added layer of privacy by allowing you to send messages that automatically disappear after a set period. This feature is perfect for discussions that you’d rather not have lingering in chat history. Here’s how to use it:
- Step 1: Open the chat where you want to enable Disappearing Messages.
- Step 2: Tap the recipient’s/group’s name at the top of the chat window to access their profile.
- Step 3: Scroll down and find the “Disappearing Messages” option.
- Step 4: Select “On” to activate the feature for that specific chat.
- Step 5: Confirm your choice, and messages sent in this chat will automatically disappear after the predetermined time (7 days) unless manually saved.
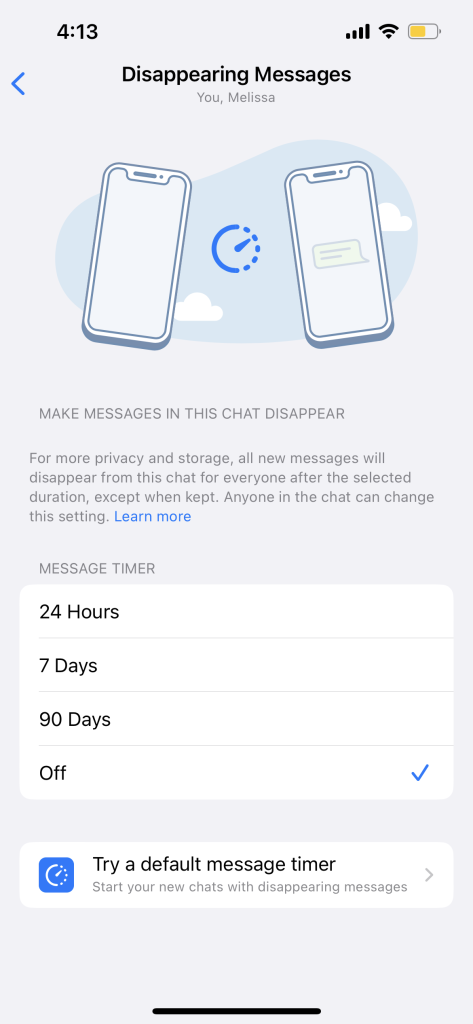
By using Disappearing Messages, you can engage in sensitive discussions or share temporary information without leaving a digital trail. It’s an excellent way to maintain privacy while communicating through WhatsApp.
In addition to mastering WhatsApp privacy settings, there’s a treasure trove of handy tips and tricks that can enhance your messaging experience. Discover these hidden gems that can make your conversations more efficient and enjoyable. From customizing notifications to using chat shortcuts, and even sending self-destructing messages, this collection of 15 WhatsApp hacks will take your messaging game to the next level. Whether you’re a casual user or a seasoned pro, these cool tricks are sure to impress and streamline your WhatsApp interactions. Check out our detailed guide on Unlock the Best WhatsApp Hacks: 15 Cool Tips and Tricks You Didn’t Know to explore these fantastic WhatsApp hacks and become a messaging maven.
In Conclusion: Empowering WhatsApp Privacy
By following these guidelines, you can harness the power of WhatsApp while retaining control over your personal information. As you connect with friends and family, prioritize your privacy and security. As technology continues to evolve, the onus is on us to adapt and ensure that our digital interactions align with our privacy preferences.
WhatsApp has transcended mere messaging, evolving into a global communication phenomenon. With its user-friendly interface and robust features, it has revolutionized the way we connect. From sharing cherished memories through multimedia to real-time conversations spanning continents, WhatsApp empowers us to bridge distances effortlessly. Discover more about the app that’s reshaping modern communication by visiting Whatsapp Website. Join the millions who have made WhatsApp an integral part of their digital lives.
]]>What is a YubiKey?
A YubiKey is a hardware security key designed by Yubico, a company renowned for its prowess in creating encryption and authentication devices. This compact device enhances digital security by adding an extra layer of protection to the traditional username-password model, employing a method known as two-factor authentication (2FA) or multi-factor authentication (MFA).
The core philosophy of YubiKey is that even if a malicious entity has your password, they can’t access your account without the physical key. It’s an idea that perfectly encapsulates the adage: simplicity is the ultimate sophistication.

How Does a YubiKey Work?
YubiKeys hinges on the concept of 2FA and MFA. These systems necessitate at least two evidence types for user authentication. First, something you know (like a password), and second, something you have (the YubiKey).
Upon logging into a service that supports 2FA or MFA with YubiKey, you input your username and password. Then, you’re prompted to insert your YubiKey or connect it to your smartphone. The YubiKey communicates a unique, one-time passcode to the service, verifying your login request.
YubiKeys also support Universal 2nd Factor (U2F), an open authentication standard that simplifies and fortifies two-factor authentication through specialized USB or NFC devices.
Here is an official article about it.
Benefits of Using a YubiKey
Enhanced Security
The primary benefit of using a YubiKey is the enhanced security it offers. By requiring a physical device in addition to a password, it protects against common cyber threats like phishing, man-in-the-middle attacks, and password reuse. Even if someone manages to steal your password, they won’t be able to access your account without the physical YubiKey.
Related What is a computer malware
Resistance to Phishing
YubiKeys are particularly effective against phishing attacks. Unlike traditional 2FA methods such as SMS or email codes, which can be intercepted or redirected, the YubiKey’s authentication cannot be replicated or stolen. This is because the key generates a new, unique code every time it’s used.
Streamlined Authentication
YubiKeys simplify the authentication process. Instead of waiting for a text message or email with a code, you simply insert the YubiKey into your device or connect it via NFC. It’s quick, easy, and doesn’t rely on you having access to your phone or email account.
Longevity and Durability
YubiKeys are designed to withstand rough handling and environments. They’re waterproof, crush-resistant, and don’t require a battery, making them more durable and longer-lasting than many other 2FA devices.
How YubiKeys Enhance Online Privacy
In the digital age, online privacy is a paramount concern. Here’s how YubiKeys can contribute to safeguarding your privacy:
Mitigating Data Breaches
Data breaches often occur when unauthorized individuals gain access to databases containing personal information. By requiring physical authentication, YubiKeys make it significantly harder for hackers to gain access to your accounts, even if they’ve obtained your username and password.
Protecting Identity
Identity theft often begins with gaining access to a person’s email or other accounts. By securing your accounts with a YubiKey, you’re adding an additional layer of defense against these attacks.
Encryption
YubiKeys also support OpenPGP and PIV (Personal Identity Verification) standards, enabling encryption and decryption of sensitive data. This means you can store your private keys on the YubiKey, further enhancing your online privacy.
Practical Steps for Using a YubiKey
Let’s look at some practical steps on how to start using a YubiKey:
- Purchase a YubiKey: Yubico offers several YubiKey models to choose from. Make sure to select the one that fits your needs and is compatible with your devices.
- Set up your YubiKey: Follow Yubico’s instructions for setting up your YubiKey with your device. The setup process will differ depending on your device and the services you wish to secure.
- Register your YubiKey with services: Most services that support 2FA will have an option for security keys in their settings. Follow their instructions to register your YubiKey.
- Use your YubiKey: Whenever you log into a service with which your YubiKey is registered, you’ll be prompted to authenticate with your YubiKey after entering your password.
- Keep your YubiKey safe: Remember, your YubiKey is now a key to your accounts. Treat it with the same care you would for your house keys or credit cards.
In conclusion, YubiKeys offer a substantial level of protection for online accounts and personal information. In an age where digital threats are increasingly sophisticated and common, investing in a YubiKey can be a powerful step towards securing your digital life. With their ease of use, robust security, and commitment to privacy, YubiKeys are a worthy addition to any security-conscious individual’sor organization’s toolkit.
Future of YubiKeys
As we move towards a more digitized world, the importance of robust security measures continues to grow. Yubico, the company behind YubiKeys, is continuously innovating to meet these needs. Future YubiKeys might have more features integrated, like biometric authentication, to further enhance security.
While YubiKeys currently supports a variety of authentication protocols, we can expect broader support for emerging standards in the future. This will make YubiKeys even more versatile and widely applicable for a range of security needs.
Additionally, as more people become aware of the importance of digital security, we can anticipate wider adoption of physical security keys. YubiKeys may become as common as house keys in the future, with people carrying them around to protect their digital identities.
The future looks bright for YubiKeys and similar technologies. As we continue to entrust more of our lives to the digital realm, tools like these will play an increasingly critical role in ensuring our information remains secure.
In conclusion, YubiKeys offer a practical, robust, and user-friendly solution for enhancing digital security. They are a testament to the role innovative technology can play in addressing some of the most pressing challenges of our digital age. Whether for personal use, business applications, or high-stakes governmental and defense scenarios, YubiKeys provide a substantial layer of protection and peace of mind in navigating the digital world.
]]>